
The 1990s saw the World Wide Web expand, creating new industries and providing previously unheard-of opportunities.. However, this era of increased connectivity also ushered in new challenges. Email accounts became targets for spam, and computer viruses wreaked havoc on corporate networks. The emergence of hacking expanded the concept of theft to include unauthorized access to computers for the purpose of stealing personal information and deceiving individuals into divulging private data. This puts at risk not only business secrets but also bank account credentials and individuals’ identities.
Regrettably, contemporary hacking threats are even more severe and sophisticated. Businesses are depending more and more on technology. the potential consequences of cyberattacks grow more severe. Fortunately, organizations have various means at their disposal to fortify their defenses and safeguard critical data from the ever-evolving tactics of hackers. For those looking to bolster their knowledge and skills in effectively countering cyber threats, considering enrolling in a reputable Cyber Security Course in Chennai can be a proactive step. This educational opportunity will equip individuals with the knowledge required in today’s complex digital environment to keep ahead of the curve and put strong cybersecurity safeguards in place.
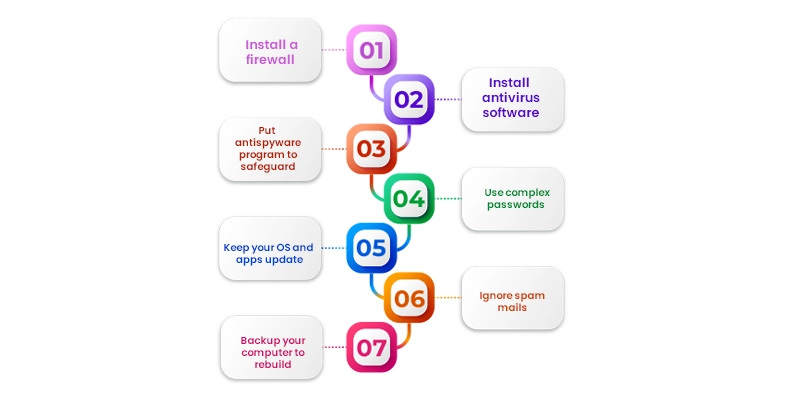
What steps can you take to keep hackers off your computer?
In the face of pervasive hacking threats such as ransomware, business email compromise scams, and data breaches, the majority of businesses continue to heavily depend on the internet for various crucial activities. This reliance spans a spectrum of operations, including tracking finances, managing inventory, executing marketing and public relations campaigns, engaging with customers, leveraging social media, and conducting essential business functions. While massive computer breaches impact large corporations equipped with robust security measures, hackers also direct their attention towards small businesses. These smaller entities may underestimate the risks associated with cybercrime and often lack the financial resources to implement expensive cybersecurity solutions. As a result, both large and small businesses find themselves navigating a complex landscape where cybersecurity is paramount for safeguarding sensitive data and maintaining operational integrity.
To protect your computer from hackers, install a firewall.
Both Windows and macOS operating systems come equipped with built-in firewalls, which are specialized software designed to establish a protective barrier between your data and external threats. Firewalls play a crucial role in thwarting unauthorized access to your business network and providing alerts in the event of intrusion attempts.
It is imperative to verify that the firewall is activated before connecting to the internet. Additionally, businesses have the option to enhance their network security by investing in hardware firewalls offered by reputable companies such as Cisco, Sophos, or Fortinet. These hardware firewalls are often integrated into broadband routers, adding an extra layer of protection to the network. For larger businesses, the option exists to acquire dedicated business networking firewalls, offering customised security solutions based on the size and unique requirements of the company. These measures collectively contribute to a robust defense against potential cyber threats.
Install antivirus software to thwart hackers
Antivirus software stands as an essential component of cybersecurity for small businesses. In the digital landscape, computer viruses and malware pose omnipresent threats. Antivirus programs such as Bitdefender, Panda Free Antivirus, Malwarebytes, and Avast are instrumental in shielding computers from unauthorized code or software that may jeopardize the integrity of the operating system. The impact of viruses can range from noticeable effects such as slowing down your computer or deleting critical files to more subtle and covert actions.
Real-time threat detection is antivirus software’s main purpose. ensuring the safety of your data. Advanced antivirus programs often offer automatic updates, fortifying your system against newly emerging viruses on a daily basis.
To maximize the efficacy of antivirus protection, it is imperative to not only install the software but also actively use it. Regularly running or scheduling virus scans is a proactive measure to maintain a virus-free computer environment and safeguard critical business data. For those who are determined to be proactive in guaranteeing the security of digital networks and systems, considering enrolling in a reputable Ethical Hacking Course in Bangalore can be a valuable step. This educational opportunity will provide insights and skills to understand potential vulnerabilities, strengthen security measures, and contribute to the overall resilience of digital infrastructure.
Put in place an antispyware program to safeguard your company
Spyware represents a type of software designed to clandestinely monitor and gather personal or organizational information. This insidious software is challenging to detect and remove, typically manifesting its presence through unwanted ads or search results with the intention of redirecting users to specific, often malicious, websites. Certain forms of spyware go to the extent of recording every keystroke, thereby gaining unapproved access to private data, including financial details and passwords.
Antispyware software specifically focuses on combating the threat posed by spyware. While standalone antispyware solutions exist, it’s worth noting that many comprehensive antivirus packages, including those from reputable providers like Webroot, McAfee, and Norton, incorporate antispyware features. These packages deliver real-time protection by systematically scanning all incoming information and proactively blocking potential spyware threats, thereby enhancing overall cybersecurity.
Use complex passwords to prevent network intrusions
Employing strong passwords is a fundamental measure for preventing network intrusions, as the strength of your passwords directly correlates with the level of difficulty hackers face in infiltrating your system.
Robust passwords typically exhibit traits such as length and complexity. It is advisable to use passwords with a minimum of eight characters, using a combination of special symbols, capital and lowercase letters, and numerals. The utilization of recognizable words or combinations, such as birthdays or easily associated information, should be avoided. Additionally, Avoid using the same password for many accounts, as this habit makes you more vulnerable.
Given the challenge of managing numerous complex passwords, employing a password manager can be a practical solution. Password managers like Dashlane, Sticky Password, LastPass, or Password Boss offer secure storage and easy retrieval of passwords, contributing to a more secure and manageable approach to password management.
Keep your OS, apps and browser updated
Regularly installing operating system updates is a critical practice for enhancing cybersecurity. These updates often incorporate essential security fixes that serve as a deterrent against hackers attempting to gain unauthorized access to and exploit your data. Similarly, keeping all installed apps up-to-date is vital, as updates frequently include security enhancements that fortify the overall resilience of the system.
Apart from upgrading the operating system and applications, paying attention to web browser security is paramount. Modern web browsers are equipped with advanced features, especially in terms of privacy and security. It is advisable to review and adjust your browser security settings to optimize protection. Techniques such as configuring the browser to prevent websites from tracking your online activities contribute to enhanced privacy. Utilizing private browsing modes or opting for browsers specifically designed with a focus on security, such as DuckDuckGo or Epic Privacy Browser, can provide additional layers of protection against online threats.
To prevent hackers from accessing your system, ignore spam
Vigilance regarding email security is crucial to avoid falling victim to phishing attacks. Be cautious when dealing with email messages from unknown sources, and refrain from clicking on links or opening attachments unless you can verify their legitimacy. While inbox spam filters are effective at identifying obvious spam, it’s essential to remain vigilant, as phishing emails have evolved to mimic familiar contacts and trusted entities, such as friends, associates, or reputable businesses like banks.
Maintaining a keen eye for anything that appears suspicious or raises doubts is a proactive approach to thwarting phishing attempts. Verify the authenticity of unexpected emails by reaching out to the purported sender through a trusted and independent means of communication to confirm the legitimacy of the message. By adopting a cautious and discerning approach, People can take major preventative measures to lower their vulnerability to phishing schemes and protect their private data.
Backup your computer to rebuild if necessary
Setting up routine backups of your company’s data is crucial for reducing the effect of any data losses or breaches. In the event of a successful computer hacking attempt or system compromise, having up-to-date backups enables quick and efficient restoration of critical information.
Both macOS and Windows provide built-in backup utilities, such as Time Machine for macOS and File History for Windows, which are effective tools to initiate regular backups. Utilizing an external backup hard drive offers a convenient and secure storage solution for these backup utilities. Alternatively, leveraging cloud-based backup systems, such as Google’s, can provide seamless and straightforward backup options, ensuring redundancy and accessibility of data even in the face of unexpected events.
By implementing a robust backup strategy, Businesses can guarantee the availability and integrity of critical data in the face of unforeseen circumstances and greatly increase their resilience to cyber threats. For those looking to deepen their knowledge and skills in fortifying digital assets against cyber threats, enrolling in a reputable Cyber Security Course in Coimbatore at FITA Academy can be a proactive step. This educational opportunity equips individuals with the expertise needed to develop and implement effective cybersecurity measures, including robust backup strategies, in today’s dynamic and challenging digital landscape.
Turn off computers to make yourself a less obvious target for hackers
Implementing periodic shutdowns of your business computers, especially during periods of inactivity or overnight, is a prudent security measure. While some businesses, particularly those running web servers or operating in a 24/7 model, may need continuous operation, others can benefit from shutting down machines during extended idle periods.
Turning off computers during downtime reduces their visibility and availability as potential hacker targets. This practice is particularly effective in breaking any established connections or potential intrusions that hackers may have initiated. By disrupting possible malicious activities during shutdowns, Businesses fortify their networks and systems with extra security.
Incorporating periodic shutdowns into your cybersecurity strategy is a simple yet effective practice to enhance the overall security posture of your business and minimize the risk of unauthorized access or compromise.
Use virtualization to protect your network
While avoiding sketchy websites is the most effective way to prevent browser-related security threats, virtualization offers an additional layer of protection for users who may interact with potentially unsafe online content. Virtualization tools, such as Parallels or VMware Fusion, allow users to run their web browsers in isolated virtual environments separate from the host operating system.
By running the browser in a virtual environment, potential threats encountered on websites are contained within that environment and do not directly impact the underlying operating system. This helps to mitigate the risk of malware or spyware affecting the main system, providing an added security measure.
For users who frequently access websites with uncertain security profiles, virtualization can serve as a valuable strategy to enhance the overall safety of their online activities and protect the integrity of their operating systems.
Protect your network to keep hackers at bay
One of the most important things you can do to protect your network from possible hacks and illegal access is to make sure your router is secure. When setting up your network, it’s important to log in to the router and configure it with a secure, encrypted password.
Default router settings often come with generic or easily guessable passwords, making them vulnerable to unauthorized access. By choosing a strong and unique password for your router, you add an essential layer of protection to prevent intruders from infiltrating your network and making unauthorized changes to the router settings.
Regularly updating and strengthening the router’s password is good cybersecurity practice, assisting in keeping your network’s integrity intact and reducing the chance of security breaches. Taking these steps ensures that your router, a critical component of your network infrastructure, is configured with the highest security standards available.
Employ two-factor authentication as an extra line of protection
Implementing two-factor authentication (2FA) provides an additional layer of security beyond passwords, significantly enhancing protection against unauthorized access. When enabled, 2FA requires users to input a numerical code, usually given together with their password during the login procedure, to a specified phone number or email address.
This extra step adds a crucial element of verification, ensuring that even if a hacker obtains the password, they would still need access to the secondary authentication method to successfully log in. 2FA is an effective strategy to mitigate the risk of unauthorized access, especially in cases where passwords alone may be susceptible to compromise.
Users are encouraged to enable two-factor authentication whenever it’s available on websites and online services to bolster the security of their accounts and protect sensitive information from potential breaches.
Use encryption to hide information from hackers
Computer encryption is an essential security feature that protects private information from unwanted access and adds another line of defence in the event that hackers breach a network.. Information is encoded using encryption so that it can only be decoded using the right decryption key.
For Windows users, BitLocker is a built-in encryption tool, while macOS users can utilize FileVault for encrypting their hard drives. Encrypting USB flash drives containing sensitive information adds an extra level of security. Virtual Private Networks (VPNs) are effective tools for encrypting web traffic, enhancing privacy and protecting data during online activities.
When engaging in online transactions, users are advised to shop only on encrypted websites, recognisable by the closed padlock icon and the “https” in the address bar. This guarantees that private data, such payment information, is transmitted securely and remains protected from potential interception. Employing encryption measures is a crucial aspect of a comprehensive cybersecurity strategy.
How can you secure your phone from hackers?
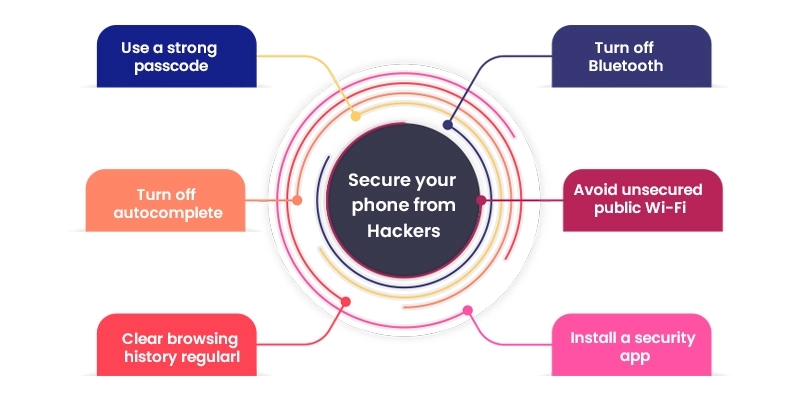
Securing your mobile device is crucial for protecting sensitive information and preventing unauthorized access. Here are some recommended measures:
Turn off Bluetooth when not in use: Disabling Bluetooth when it’s not actively in use reduces the risk of potential security vulnerabilities. Leaving Bluetooth enabled but idle can create an entry point for hackers.
Avoid unsecured public Wi-Fi: Public Wi-Fi networks without password protection lack security features, making them susceptible to cyber threats. When working remotely, use secured networks or a Virtual Private Network (VPN) for added protection.
Install a security app: Utilize security apps on your mobile device, similar to those employed on computers. Popular options like Avast and Bitdefender provide additional layers of defense against malware and other security threats.
Use a strong passcode: Opt for a randomly generated, six-number passcode instead of easily guessable codes like 0000 or 1234. A strong passcode enhances the security of your device.
Turn off autocomplete: While autocomplete is convenient, it poses a risk of inadvertently revealing sensitive information to hackers. Disable autocomplete to prevent the automatic completion of personal details.
Clear browsing history regularly: Just like on a computer, mobile browsers store browsing history, cookies, and cached files. Regularly clearing this data minimizes the information available to hackers in case of a security breach.
Implementing these practices helps fortify the security of your mobile device, safeguarding personal and business-related data from potential cyber threats. If you want to know more about the latest interview question for Ethical Hacker, Check out Ethical Hacking Interview Questions and Answers, which will help you get an insight into the job interview question, skills and experience.
What are Computer Hackers?
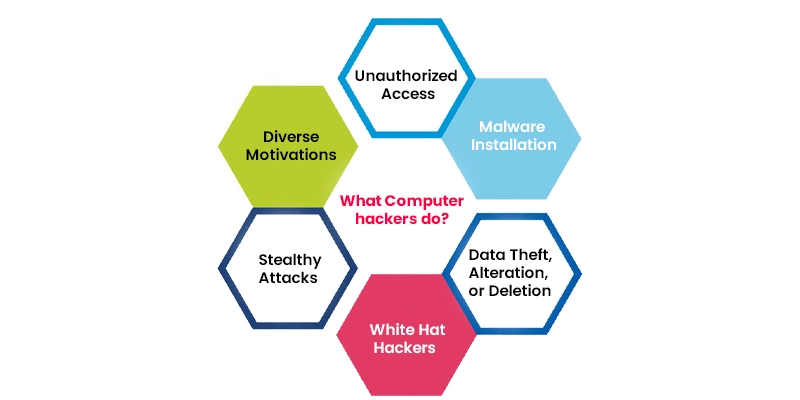
Computer hackers, also known as cybercriminals, employ various tactics to gain unauthorized access to internet-connected devices with the intent of stealing, altering, or deleting information. Here are some common aspects associated with computer hacking:
Unauthorized Access: Hackers exploit vulnerabilities in devices, networks, or software to gain unauthorized access. This can involve exploiting weaknesses in security protocols, software bugs, or leveraging social engineering techniques to trick users into revealing sensitive information.
Malware Installation: Malicious software, commonly referred to as malware, is a key tool for hackers. Malware includes viruses, ransomware, spyware, and other types of harmful software. Malware can carry out a number of tasks after it is installed on a system., such as stealing data, monitoring activities, or damaging system files.
Data Theft, Alteration, or Deletion: The primary goals of many hackers are to gain access to valuable data. This could include personal information, financial details, or business-critical data. In some cases, hackers may alter or delete data to cause disruption or financial harm.
White Hat Hackers: Some individuals, known as white hat hackers or ethical hackers, are hired by companies to identify and rectify security vulnerabilities. Their goal is to strengthen break the security protocol by finding and fixing weaknesses before malicious hackers exploit them.
Stealthy Attacks: In many cases, hackers operate discreetly, attempting to go undetected for as long as possible. This allows them to gather valuable information or maintain control over compromised systems without alerting the device owner.
Diverse Motivations: Hackers may have different motivations, including financial gain, industrial espionage, political motives, or simply causing disruption. The motives often influence the methods employed and the targets chosen.
To protect against computer hacking threats, individuals and businesses must adopt robust cybersecurity measures, including firewalls in computers used for antivirus software, regular software updates, secure passwords, and employee training to recognize and avoid social engineering tactics. For those interested in taking a proactive approach to cybersecurity and understanding the techniques employed by ethical hackers, considering enrolling in a reputable Ethical Hacking Course in Pondicherry can be a valuable step. This educational opportunity provides individuals with the knowledge and skills to identify vulnerabilities, assess security measures, and support the general robustness of digital systems.
Why do hackers breach networks and devices?
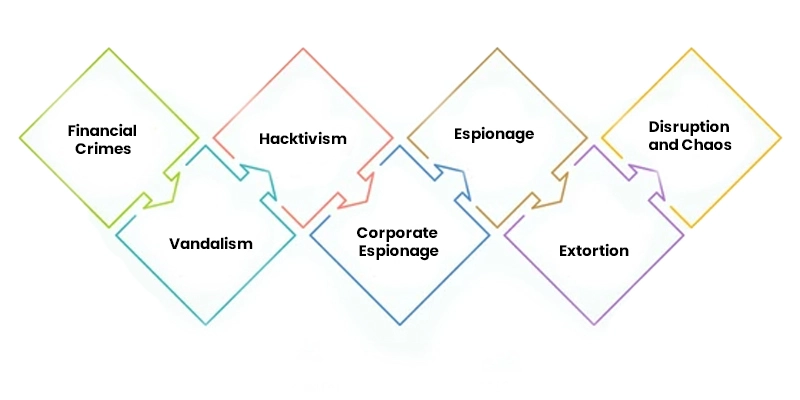
Hackers have a multitude of objectives for breaking into devices and networks, from advocacy to monetary gain. Here are some common reasons why hackers engage in such activities:
Financial Crimes
Hackers may steal credit card numbers, bank account information, or other financial data to commit fraudulent transactions and financial crimes.
Identity Theft: Obtaining personal information allows hackers to commit identity theft, which can lead to various forms of financial fraud.
Vandalism
Some hackers engage in vandalism to showcase their skills, make a statement, or gain recognition within the hacking subculture.
Website Defacement: Hackers may deface websites or disrupt online services to express a political or social message.
Hacktivism
Certain hackers, known as hacktivists, target organizations or websites to promote political or social causes. Their actions are often intended to raise awareness or protest specific issues.
Corporate Espionage
Companies may be targeted by hackers seeking to steal sensitive information, trade secrets, or intellectual property. One could take advantage of this information to obtain a competitive edge or to make money.
Espionage
Some hackers, often backed by nation-states, engage in cyber-espionage to gather intelligence, monitor political adversaries, or disrupt the operations of other nations.
Extortion
Hackers deploy ransomware to encrypt files or systems, demanding payment for their release.In this type of extortion, victims are made to pay a ransom in order to get their data back..
Disruption and Chaos
In some cases, hackers may target systems or networks simply to create chaos, disrupt operations, or cause inconvenience without a specific motive. Understanding the diverse motivations behind computer hacking is crucial for developing effective cybersecurity strategies. Individuals and organizations must implement robust security measures to safeguard against the various threats posed by hackers with different agendas. For those seeking to deepen their understanding of cybersecurity and enhance their ability to effectively break the security measures, consider enrolling in a reputable CCNA Course in Chennai. The knowledge and abilities gained from this educational opportunity will be invaluable in navigating the intricate world of network security and thwarting any potential cyber threats.
