Course Highlights and Why Ethical Hacking Course in Chennai at FITA Academy?
Upcoming Batches
- 11-05-2026
- Weekdays
- Monday (Monday - Friday)
- 14-05-2026
- Weekdays
- Thursday(Monday - Friday)
- 16-05-2026
- Weekend
- Saturday (Saturday - Sunday)
- 18-05-2026
- Weekdays
- Monday (Monday - Friday)
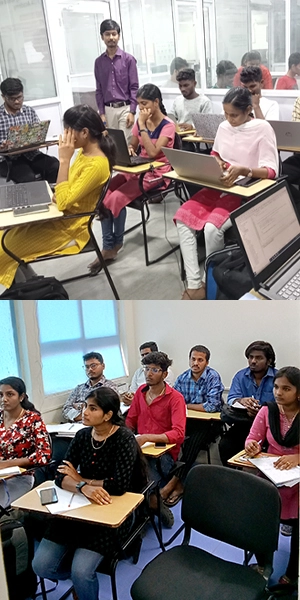
Classroom Training
- Get trained by Industry Experts via Classroom Training at any of the FITA Academy branches near you
- Why Wait? Jump Start your Career by taking the Ethical Hacking Course in Chennai!
Instructor-Led Live Online Training
- Take-up Instructor-led Live Online Training. Get the Recorded Videos of each session.
- Travelling is a Constraint? Jump Start your Career by taking the Ethical Hacking Online training!
Ethical Hacking Course Objectives
Ethical Hacking Advanced
- Find active and passive techniques to prevent footprinting and become familiar with enumeration and countermeasures.
- Comprehend steganography and its approaches for attacks and track concealing methods.
- Web server attacks, Web applications hacking techniques, and Countermeasures.
- Learn about advanced topics in SQL injection attacks, including identification tools, wireless security encryption, and cracking strategies.
- Know IDS, IPS, firewalls, and honeypots for strong Network Security.
- Thus, get familiar with encryption cyphers, different kinds of attacks, new-generation countermeasures, and social engineering methods.
- Implementing the techniques via the capstone exercise in the Certified Ethical Hacker Course in Chennai at FITA Academy.
Ethical Hacking Expert
- Learn about penetration testing, roadmap and security audit.
- Advanced searching and OSINT.
- Explore some tools, including the social engineering toolkit, Maltego, FOCA, and Shodan.
- Check up on reporting, technical auditor, and information security auditor.
- Get information about OWASP and learn more about critical vulnerabilities.
- Simulation of the critical vulnerability and simulation of its countermeasure.
- It also helps you practice the techniques and perform different capstone projects in our Certified Ethical Hacker Course in Chennai.
Syllabus
ETHICAL HACKING ADVANCED - Introduction to Ethical Hacking
- What is Hacking?
- What is Ethical Hacking?
- What is the difference between both
- What are the Learning Scope
- 5 Phases of Ethical Hacking
FootPrinting (Reconnaissance-Passive)
- Types of Footprinting
- Footprinting Tools and Countermeasures
Enumeration (Reconnaissance - Active)
- Enumeration Techniques
- Enumeration Countermeasures
Network Scanning
- Network Scanning Technique
- Network Scanning Countermeasures
System Hacking Methodology
- System Hacking methodology
- Steganography
- Steganalysis Attacks
- Covering Tracks
Virtual Machine
- Installation of VM's in Windows and MAC
- Configuration of VM's and Installing OS
- Installing Software
Kali Linux
- Kali Linux Installation
- Working with Kali Linux
- Password Hacking for Zip Files and PDF Files
Metasploit
- Introduction to Metasploit
- Working with Metasploit
- Windows Hacking and Advanced Techniques
Tools - N-map
- Scanning using Nmap Tool
- Advanced Commands and Techniques
Burp-Suite
- Introduction
- Installation
- Configuring burp-suite with browsers
- Working with burp-suite
Sniffing
- What is Sniffing
- Packet Sniffing Techniques
- How to defend against Sniffing
Malware Threats
- Types of Malware
- Types of Trojans
- Trojan Analysis
- Trojan Countermeasures
Virus and Worms
- What is Virus and How it Works?
- Virus Analysis
- Computer Worms
- Malware
- Analysis Procedure and Countermeasures
DoS and DDoS
- What is Denial of Services (DoS)
- What is Distributed Denial of Services (DDoS)
- Types of Attacks
- DoS/DDoS Attack Techniques
- Botnets
- DDoS Attack Tools
- DoS/DDoS Countermeasures
Session Hijacking Techniques
- Session Hijacking Techniques
- Countermeasures
Servers Attacks - Web Server, File Servers
- Different Types of Web server Attacks
- Attack Methodology and Countermeasures
Hacking Web Applications
- Different Types of Web Application Attacks
- Web Application
- Hacking Methodology and Countermeasures
SQL Injection Attacks
- SQL Injection Attacks
- Injection Detection Tools
Wireless Networks Attacks
- Wireless Encryption
- Wireless Cracking Methodology
- Wireless Cracking Tools
- Wireless Security Tools
IDS, IPS, Firewalls, and Honeypots
- Firewall
- Intrusion Detection System (IDS)
- Honeypot Evasion Techniques
- Evasion Tools
- Countermeasures
Cloud Computing Techniques
- Various Cloud Computing Concepts
- Cloud Computing Threats
- Cloud Computing Attacks
- Security Techniques and Tools
Cryptography
- Different Types of Cryptography Ciphers
- Public Key Infrastructure (PKI)
- Cryptography Attacks
- Cryptanalysis Tools
Social Engineering
- What is Social Engineering
- Phishing Emails
- Types of Social Engineering Attacks
- Advanced Techniques
- Countermeasures
Further Learning
Career and Opportunities
ETHICAL HACKING EXPERT - Introduction
- Introduction
- Penetration Testing
- Various Types of Penetration Testing
- Penetration Testing Roadmap
- Security Audit
Building and Setting Up the Laboratory
- Why set up your Own Lab
- Hardware, Software Requirements
- Metasploitable Linux
- OWASP Broken Web Applications
- Windows Systems as Victim
Virtual Machine
- Installation of VM's in Windows and MAC
- Configuration of VM's and Installing OS
Kali Linux
- Kali Linux Installation
- Working with Kali Linux (GUI)
- Working with Kali Linux (CLI)
- Set Up Kali Linux from ISO File
Gathering Information
Google HDB
- Google Search
- Using Google Keywords for search finetuning
- Advanced Search Techniques
OSINT - OSINT (Open Source Intelligent)
- Introduction to Information Gathering
- Using Search Engines to Gather Information
- Search Engine Tools: SiteDigger and SearchDiggity
- Shodan
- Gathering Information About the People
- Web Archives
- FOCA - Fingerprinting Organisations with Collected Archives
- Fingerprinting Tools: The Harvester and Recon-NG
- Maltego - Visual Link Analysis Tool
Social Engineering - Techniques
- Social Engineering Terminologies
- Malware - Terminologies
- Social Engineering Toolkit (SET) for Phishing
- Sending Fake Emails for Phishing
- Voice Phishing: Vishing
Scanning and Enumeration Using Advanced Tools
- Installation and Configuration
- Advanced Vulnerability Scanning Techniques
- Preventing Complex Attacks
- Effective use of the Tool to identify Weakness
Tools
- Nessus Tool
- Qualys Tool
- N-Map
- Burp-Suite
- Nikto
- Dirb
Exploitation
- Exploitation Terminologies
- Exploit Databases
- Manual Exploitation
- Exploitation Frameworks
- Metasploit Framework (MSF)
- Introduction to MSFConsole
- MSF Console & How to Run an Exploit
- Introduction to Meterpreter
- Gaining a Meterpreter Session
- Meterpreter Basics
Metasploit Framework for Penetration Testing
- Working with Metasploit
- Windows Hacking
- Creation of Malicious Executable
- Payload crafting like .exe .apk etc
- MSF Venom
- The veil to Create Custom Payloads
- TheFatRat - Installation and Creating a Custom Malware
- Embedding Malware in PDF Files
- Embedding Malware in Word Documents
- Embedding Malware in Firefox Add-ons
- Empire Project in Action
- Exploiting Java Vulnerabilities
Password Cracking
- Password Hashes of Windows Systems
- Password Hashes of Linux Systems
- Classification of Password Cracking
- Password Cracking Tools in Action: Hydra, Cain, and Abel, John the Ripper…
Post Exploitation
- Persistence: What is it?
- Persistence Module of Meterpreter
- Password Hacking for ZIP File and PDF Files
- Removing a Persistence Backdoor
- Next Generation Persistence
- Meterpreter for Post-Exploitation with Extensions: Core, Stdapi, Mimikatz...
- Post Modules of Metasploit Framework (MSF)
- Collecting Sensitive Data in Post-Exploitation Phase
OWASP Top 10 Vulnerability
- Introduction about OWASP
- Top 10 Latest Vulnerabilities
- Practical session for the Critical Vulnerabilities
- Countermeasures
Information Security Audit
- What is Information Security Audit
- Technical Audits
- Physical Audits
- Administrative Audits
- Audit Planning and Preparation
- Establishing Audit Objectives
- Auditing Application Security
Audit Reporting
- Reporting
Ethical Hacking Course Trainer Profile
- The trainers of the Ethical Hacking Course in Chennai at FITA Academy are seasoned professionals in top companies.
- The trainers keep themselves updated with the current updates in the industry so that students learn about relevant and in-demand skills.
- The aim of ethical hacking trainers is to provide practical learning experiences.
- They ensure that students gain in-depth knowledge through real-time projects and hands-on training.
- Our trainers offer regular doubt-clearing and review sessions to reinforce each concept.
- The trainers of our Ethical Hacking Course offer assessments, track the performance and indicate achievements.
Learn at FITA Academy & Get Your
Dream IT Job in 60 Days
like these Successful Students!
Student Success Story of Ethical Hacking Course in Chennai
Satvik, after completing B.tech – IT, wanted to work in IT as an ethical hacker. So, he started searching for the Best Ethical Hacking Institute in Chennai and discovered FITA Academy, a top IT Institute in Chennai. He visited his nearest branch and enquired about the course with our coordinators. Satisfied with the features and benefits of the course, he decided to join the course.
He attended all the classes, performed well in assessments and then progressed to work on live projects under the guidance of expert trainers. He completed the course and took placement training at FITA Academy.
After interview preparation, he attended an interview with NTT Data and showcased his knowledge in ethical hacking gained at FITA Academy. Eventually, he secured a position as an ethical hacker at NTT Data, with a salary package of 3.2 LPA.
Key Features
FITA Academy empowers individuals with industry-relevant skills through expert-led training, transforming careers with hands-on experience.
Expert Trainers
Learn from industry professionals with hands-on experience.
Real-Time Projects
Gain practical exposure by working on live projects.
Certification
Get certified from FITA Academy and become job-ready.
Affordable Fees
High-quality courses available at a low budget.
Flexible Learning
Choose online/classroom, timings, and learning pace.

Placement Support
Access 3000+ companies for career opportunities.
Why Learn Ethical Hacking Course in Chennai at FITA Academy?
Live Capstone Projects
Real time Industry Experts as Trainers
Placement Support till you get your Dream Job offer!
Free Interview Clearing Workshops
Free Resume Preparation & Aptitude Workshops

Ethical Hacking Certification Training in Chennai
Once you finish the Certified Ethical Hacker Course in Chennai at FITA Academy, we will provide a valuable certification. This showcases that they have a strong grasp of crucial concepts and get exposure to the tools. Including this certificate in your resume makes your profile strong.
Benefits of taking an Ethical hacking course in Chennai at FITA Academy
- Career Advancement: With an ethical hacking course, you can take your career to the next level in Cyber Security related roles.
- Job Security: Employers recruit from various sources, and obtaining a certification distinguishes you as a competent expert. By mastering software tools, you become a subject matter expert and might even provide consulting services for other employers. Obtaining certification as an ethical hacker keeps you updated in the constantly changing technology landscape.
- Professional Development: FITA Academy aims to cultivate students into effective leaders by providing knowledge of contemporary technology like Artificial Intelligence in Cyber Security and encouraging critical thinking abilities, enabling them to make well-informed career choices.
- Practical Learning Experience: Students will explore computer security thoroughly, discovering how hackers infiltrate systems. By comprehending harmful software, you can identify and protect yourself from them efficiently.
Have Queries?
Talk to our Career Counselor for more Guidance on picking the right Career for you!
Placement Session & Job Opportunities
After completing Ethical Hacking Course in Chennai




As modern threats and attacks emerge, every organisation is in need of ethical hackers to protect data and networks. Additionally, demand for this profession with these skills is expected to increase. Organisations are increasingly cautious about data protection across industries due to the rise in attacks. Therefore, identifying ethical hackers to protect corporate data and strengthen security systems is essential.
Our placement ecosystem operates as an “Offensive Security Talent Incubator,” engineered to bridge the critical gap between technical skill and Executive Crisis Management. As organizations transition toward Cloud-Native and Decentralized Architectures, the demand for specialists who can navigate Identity-Centric Security has reached a record high. We don’t just facilitate job matches; we transform our students into Cyber Strategists who can communicate technical risk to boardroom stakeholders.
With Nasscom projecting a yearly need for a minimum of 77,000 ethical hackers in India, our Ethical Hacking Course with Placement in Chennai at FITA Academy can help you unlock high-paying jobs. Ethical Hacker Salary for Freshers typically range from 3.8 LPA to 4.9 LPA.
“We offer 100% placement support upon completing our Ethical Hacking Course.”
Various industries such as information technology and IT-enabled services (ITES) firms, financial firms, e-commerce companies, government organizations, consulting businesses, banks, security services, defence businesses, telecommunication companies, aviation industries, airlines, immigration services, forensic sciences, healthcare and cloud service vendors are searching for Certified Ethical Hackers. With an Ethical Hacking Tutorial, you can gain in-depth knowledge needed to thrive in the field.
Through our exclusive partnerships with over 3,000 global firms. We provide intensive coaching on Executive Presence, ensuring you can manage real-world breach simulations with the poise of a seasoned expert. This holistic approach to professional development is why our graduates are the preferred choice for multinational firms. Given the premium mentorship and specialized toolsets provided, the Ethical hacking course fees at FITA Academy are considered highly reasonable, offering an unmatched return on investment in the high-growth field of Autonomous Threat Defense.
Career Prospects after completing an Ethical Hacking Course in Chennai
Network Security Engineer
These are essential professionals in the design and policy implementation as well as the enforcement and enhancement of network security. Mainly used by big businesses or government bodies, these specialists are crucial in improving general security systems. They create and oversee various networks as a network of dedicated organisations in public and commercial fields. To excel in this position one needs a solid knowledge of network, management, and ethical hacking methodologies. FITA Academy has introduced Ethical Hacking Classes in Chennai suitable for those wishing to start practising as network security engineers. Our Ethical Hacking Syllabus is designed so that you will be in a better position to understand the complications of the cyber world and how you can protect vital details.
Network Security Administrator
NSAs perform numerous tasks, including managing user access control mechanisms, maintaining networks, and implementing security improvements. NSAs must be well-informed about Ethical Hacking concepts to maintain good network security. Safeguarding networks requires a combination of strong software engineering skills and high ethical standards. Since the field of network security presents several great opportunities, you can become a Network Security Admin after taking a Hacking Course in Chennai.
Security Consultant
Security consultants are involved in almost every organisation, as their skills allow them to provide clients with the best experience. FITA Academy offers Ethical Hacking Course, which offers opportunities to those wanting to contribute to the vast business field. A security consultant’s chief responsibility is protecting the network from various hazards.
Performing various types of security assessments, such as penetration testing, vulnerability assessment, code review, intrusion detection, incident response, and reverse of an application or a system is the primary activity of a security consultant. The above tasks are best handled by a professional security consultant who needs to prepare sound reports.
Network Associate
With a CCNA certification, you can become a network associate. In this role, you will be required to ensure the continuity and optimisation of various networks. Some of the roles include designing, migrating, and installing networks and identifying and resolving data integrity issues. They also execute security features, control access lists, and monitor routers and switches. To help you master this field, it’s essential to study the necessary concepts and read Ethical Hacking Books or choose the right course to commence your ethical hacking journey.
Srinisha
Enrolled at FITA Academy for Ethical Hacking course. The practical sessions are really helpful and the effort of my trainer is really appreciated. Everyone was extremely helpful, especially the coordinators. I would surely recommend this platform to freshers and thanks to this team.
Jai Shankar
Upon enrolling for the Ethical Hacking Course in Chennai at FITA Academy, I have a clear understanding of the hacking concepts. Also, my Trainer was a real-time professional from the Cyber Security field and he provided numerous valuable insights into the Ethical Hacking practices and techniques to us. A sincere thanks to him.
Shekar
Overall good training experience at Ethical Hacking Course in Chennai at FITA Academy. I am satisfied that I choose the right platform. All the modules were covered within the mentioned time also re-scheduling of classes was done at ease over here. Thanks, FITA Academy!.. You are really doing a good job!!
Pankaj Tripathi
Ethical Hacking Training in Chennai at FITA Academy was excellent. What I liked more is the approach of the Trainer towards the students. Further, the support team coordinated the classes well with the best training faculty. Freshers can definitely opt for this platform to have a holistic understanding of the Ethical Hacking practices.
Aparna
My overall experience at Ethical Hacking Training at FITA Academy was good. Hands-on Training on real-time security practices along with the Ethical hacking tools was provided by my trainer. Gained good knowledge of Ethical Hacking practices and techniques.
Ajay Kumar
FITA Academy is the right platform to get Ethical Hacking Training under industry experts. The classes were engaging and informative, Here I gained extensive knowledge about Ethical Hacking Tools and their benefits. I would surely recommend Ethical Hacking Course in Chennai for freshers. Special thanks to my trainer who has answered all my queries.
Our Students Work at

Frequently Asked Question (FAQ) about Ethical Hacking Course in Chennai
- We have highly-experience trainers who are actively in the field of ethical hacking and cyber security.
- FITA Academy has successfully placed more than 1,00,000 students.
- FITA Academy costs affordable Ethical Hacking Course fees in Chennai.
- With flexible batch timing students are allowed to attend weekdays and weekends.
- We provide 100% placement assistance, Interview Tips and Corporate Training for course participants.
- We offer 100% placement training to our students as we have tie-ups with over 3000 companies. In addition, we have an active placement cell that helps in resume building and informs about job openings in the field.
- Also, You can find guidance for preparing the most common questions asked Ethical Hacking Interview Questions and Answers.
General Q & A about Ethical Hacking Course in Chennai
What is the salary of an ethical hacker in Chennai?
What is the best course for ethical hacking?
What is the ethical hacking course in Chennai fees?
What is the minimum time taken to learn ethical hacking?
Is ethical hacking a good profession?
Is ethical hacking a good course?
Is it possible to work at home as an ethical hacker?
How much you get paid as Ethical Hacker in Google?
Do banks hire ethical hackers?
Will AI replace hackers?
What code is used in ethical hacking?