
Amazon Web Services (AWS) stands out as a premier cloud computing platform, providing users with a secure virtual environment for deploying and managing applications. In comparison to traditional on-premises setups, AWS offers enhanced data protection at a more cost-effective scale. The platform is renowned for its commitment to security, scalability, and economic advantages.
What is AWS Security?
AWS Security encompasses the foremost concern for cloud security within the AWS platform. Hosting your environment in the cloud ensures it resides within a data center or network architecture meticulously designed to adhere to the stringent security standards of even the most security-sensitive organizations. Furthermore, this elevated level of security is accessible through a pay-as-you-go model, eliminating upfront costs and presenting a more cost-effective option when compared to on-premises environments.
Numerous security services are at one’s disposal, with AWS extensively employing several, including:
- IAM (Identity and Access Management)
- Key Management System (KMS)
- Cognito
- Web Access Firewall (WAF)
IAM empowers you to meticulously govern access to AWS services and resources. This robust system allows you to create groups, granting specific users or groups access to designated servers or, conversely, restricting their access to certain services. This ensures a highly secure approach to managing access within your AWS environment. For in-depth learning and hands-on experience with AWS services, consider enrolling in AWS Training in Chennai, where you can gain valuable insights and skills to navigate the AWS ecosystem effectively.
Why IAM?
In the pre-AWS and IAM era, the sharing of passwords within corporate environments often took place through insecure means, such as phone conversations or email exchanges. Typically, a singular admin password was in use, stored in a fixed location, or entrusted to a single individual with reset capabilities. Access to this password required a phone call to the designated person, introducing significant security vulnerabilities. This practice lacked robust security measures, as anyone within proximity could potentially eavesdrop, acquiring the admin password and unauthorized access to the system and sensitive information.
Presently, a more secure communication tool, Slack, a third-party application hosted on AWS, has emerged. This application facilitates secure document sharing, eliminating the risks associated with eavesdropping during the communication process.
What is IAM?
AWS Identity and Access Management (IAM) stands as a web service dedicated to the secure management of access to AWS resources. It provides the capability to establish and govern services for user authentication, ensuring a robust framework for controlling access to designated individuals utilizing your AWS resources. IAM is instrumental in creating and enforcing access policies, thus contributing to a secure and well-regulated environment for the utilization of AWS services.
How Does IAM Work?
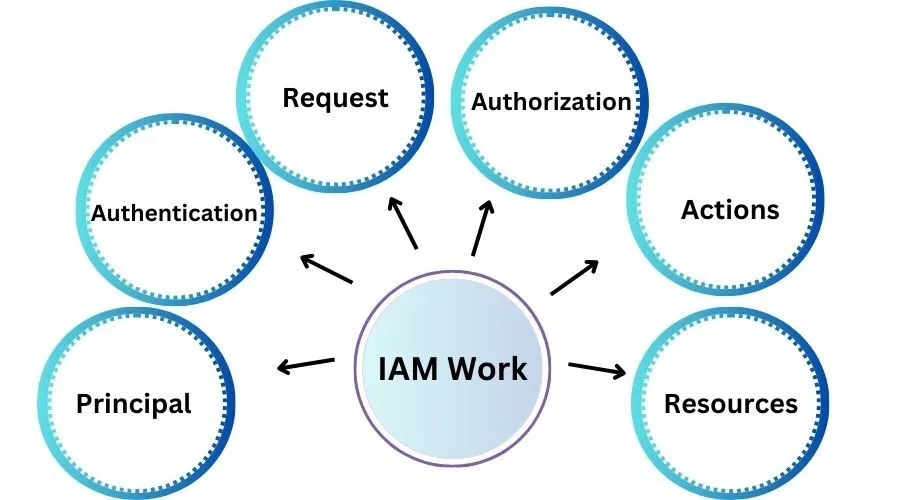
The IAM workflow encompasses six key elements:
1. Principal
An entity capable of executing actions on an AWS resource. This could be a user, a role, or an application.
2. Authentication
The process of validating the identity of the principal attempting to access an AWS product. The principal must furnish the necessary credentials or keys for authentication.
3. Request
A principal initiates a request to AWS, specifying the action and the resource on which it should be performed.
4. Authorization
By default, all resource access is denied. IAM authorizes a request only if every aspect aligns with a matching policy. Following authentication and authorization, AWS approves the requested action.
5. Actions
Operations performed to view, create, modify, or delete a resource.
6. Resources
A collection of actions that can be executed on a resource associated with your AWS account.
Components of IAM
IAM comprises additional fundamental components. Initially, there is the “user,” and multiple users collectively constitute a “group.” “Policies” serve as the mechanisms that either permit or deny a connection based on specified rules.
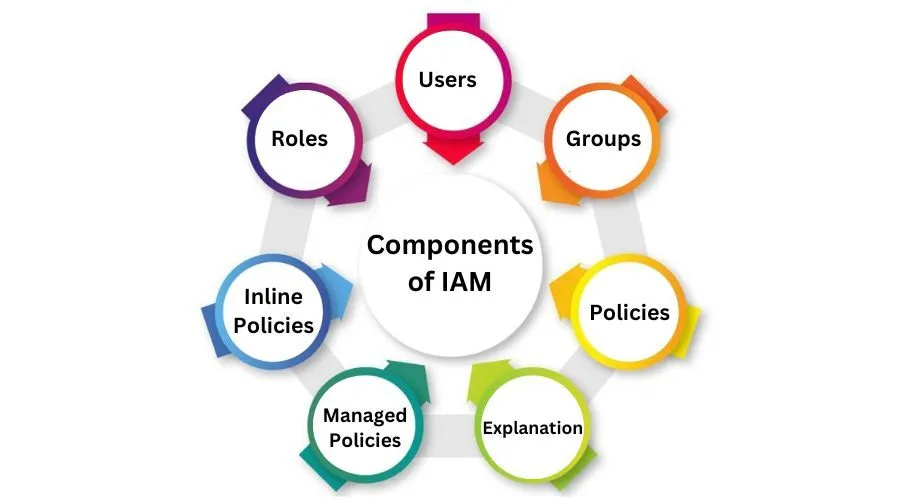
Furthermore, “roles” represent temporary credentials that can be assumed by an instance as required. To gain comprehensive insights into AWS services such as IAM and strengthen your expertise, consider enrolling in an AWS Course in Coimbatore, where you can acquire valuable knowledge and hands-on experience in utilizing Amazon Web Services.
Users
IAM users function as distinct identities with associated credentials and permissions within the AWS ecosystem. These users can represent either actual individuals or applications requiring access. IAM facilitates the secure administration of AWS service access by assigning a unique IAM username to each employee or application in your organizational setup. Each IAM user is exclusively linked to a specific AWS account, ensuring a clear delineation of access and permissions.
Upon creation, a new IAM user lacks default authorization for any AWS actions. This intentional restriction serves as a security measure. The inherent advantage of the one-to-one user specification lies in the ability to tailor permissions on an individual basis. This granular control allows for the precise assignment of permissions to each IAM user, aligning with the principle of least privilege.
IAM users streamline the process of managing access, promoting a secure and customized approach to AWS service utilization within an organization.
Groups
An assemblage of IAM users forms an IAM group, offering a streamlined approach to managing permissions for multiple users concurrently. IAM groups provide a means to designate permissions at a collective level, ensuring that any permissions allocated to the group extend automatically to each individual user within that group. Simplifying administrative tasks, the management of IAM groups proves to be straightforward. Permissions set for the group are seamlessly and instantly applied to all users encompassed within it.
The efficiency of group management is particularly evident when considering the ease of permissions inheritance. When a new user is added to a group, they effortlessly inherit all policies and permissions previously assigned to that specific group. This streamlined process not only expedites user onboarding but also reduces administrative overhead significantly. By centralizing and orchestrating permissions through IAM groups, organizations can enhance security measures, promote consistency in access control, and efficiently manage user entitlements within the AWS environment.
Policies
An IAM policy serves as a pivotal tool for defining permissions and regulating access to AWS resources. These policies are stored within AWS in the form of JSON documents. Within these policy documents, permissions are meticulously articulated, delineating who has access to specific resources and specifying the actions they are authorized to undertake.
For instance, a policy might grant an IAM user access to a particular bucket within Amazon S3. The policy document encapsulates crucial details such as:
- Identity Specification: Outlining who is granted access.
- Action Authorization: Enumerating the actions that the specified user is permitted to execute.
- Resource Accessibility: Designating which AWS resources the user can access.
Furthermore, IAM policies can also incorporate temporal considerations, specifying when access permissions are valid. This comprehensive approach to policy definition empowers organizations to precisely control and tailor access privileges, promoting a secure and finely tuned AWS environment.
In JSON format that would look like this:
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": "s3:*",
"Resource": [
"arn:aws:s3:::your-bucket-name",
"arn:aws:s3:::your-bucket-name/*"
]
}
]
}
Explanation
Version: Specifies the version of the policy language. In this case, it’s “2012-10-17,” which is the current version.
- Statement: An array containing one or more statements that define the permissions. In this example, there’s only one statement.
- Effect:Specifies whether the statement allows or denies access. Here, it’s set to “Allow.”
- Action: Specifies the action or actions that the policy allows. In this case, it allows all actions (s3:*) on the specified bucket.
- Resource: Specifies the AWS resources to which the actions apply. The provided ARNs (Amazon Resource Names) specify the bucket and its contents.
This policy, when attached to an IAM user, would grant full access to the specified S3 bucket. It’s important to note that this is a broad example, and in practice, you would typically tailor policies to provide the least privilege necessary for users or roles to perform their required tasks. To delve deeper into cloud computing concepts such as IAM and gain practical skills, consider exploring Cloud Computing Training in Chennai, where you can enhance your knowledge and proficiency in cloud technologies.
Two distinct types of policies govern access control within AWS: managed policies and inline policies.
Managed Policies
These are default policies that can be attached to multiple entities like users, groups, and roles across your AWS account. Regardless of whether they are AWS-managed or customer-managed, managed policies are autonomous, identity-based policies. They provide a stand-alone approach, being associated with multiple users and/or groups. AWS-managed policies are crafted by AWS, while customer-managed policies are customized by the AWS account holder to meet specific organizational needs. The advantage of managed policies lies in their ability to be centrally administered and effortlessly applied to various entities, ensuring consistency in access permissions.
Inline Policies
In contrast, inline policies are policies created and directly embedded into a singular entity, be it a user, group, or role. Unlike managed policies, inline policies are specific to an individual entity. This means that the policy is intricately tied to the entity it is created for and doesn’t exist independently. Inline policies provide a more granular level of control, allowing for precise customization of permissions for a particular entity without affecting others. However, this customization comes at the cost of potentially increased administrative complexity when managing policies for numerous entities.
Roles
An IAM role constitutes a set of permissions that delineate the actions permissible or restricted for an entity within the AWS console. Comparable to a user, an IAM role is versatile in that it can be accessed by various entities, be they individuals or AWS services. Notably, the permissions associated with IAM roles are characterized by their temporariness, as they provide temporary credentials.
Consider scenarios where you want to grant a mobile app access to AWS resources without storing sensitive key information. IAM roles prove invaluable in such cases. Similarly, if you wish to extend resource access to a user already authenticated outside of AWS, such as through Google or Facebook, IAM roles offer a seamless solution. Furthermore, IAM roles facilitate the provision of services or resource access to individuals in your account, including temporary access for third parties like consultants or auditors. This temporary access ensures that these entities, though not permanent users, can fulfill specific roles within your environment as needed.
Features of IAM
IAM encompasses a suite of key features that enhance access management within the AWS ecosystem:

Account Access Customization
IAM empowers the creation of distinct usernames and passwords for individual users or resources, facilitating the delegation of access within the AWS account.
Precise Permission Controls
IAM provides the capability to impose specific restrictions on requests. For instance, permissions can be configured to grant users the ability to download information while concurrently restricting their capacity to update data through defined policies.
Enhanced Security via MFA
IAM supports Multifactor Authentication (MFA), augmenting security by necessitating users to furnish their username, password, and a one-time password from their mobile device.
Identity Federation Support
IAM accommodates identity federation, allowing reliance on pre-authenticated methods such as Facebook or Google accounts. This streamlines access based on trusted authentication, fostering a unified password approach for both on-premises and cloud environments.
Cost-Efficient Security
IAM security features incur no additional charges. The creation of additional users, groups, or policies does not result in additional costs.
PCI DSS Compliance Adherence
IAM aligns with the Payment Card Industry Data Security Standard (PCI DSS), ensuring compliance with rigorous information security standards for organizations handling major credit card brands.
Flexible Password Policy
IAM provides a versatile password policy, enabling remote password management with features such as resets and rotations. Administrators can establish rules, including password complexity requirements and login attempt limits, fortifying security measures within the IAM framework. For a comprehensive understanding of AWS and to enhance your skills in cloud technologies, consider enrolling in the AWS Course at FITA Academy, where you can gain hands-on experience and expertise in AWS.
Create an S3 Bucket Using the MFA Feature
In the concluding section of this blog, we will synthesize the presented information to address a fundamental problem scenario:
Problem Statement
To establish an S3 bucket for a company wherein each user possesses the capability to read and write data, with the added layer of multifactor authentication.
Task
The primary objectives are to create policies and allocate permissions for both an individual user and a specified group.
Provide Read and Write Access for the Developer Group
Enable members of the developer group to read and write data.
Implementation: Formulate and assign policies that grant the requisite permissions to the designated group.
User-Specific Policy for S3 Object Operations
Define a policy for a user allowing read access while denying write permissions for objects within an S3 bucket. Construct a policy tailored to the user’s requirements, allowing them to read objects but restricting write operations on the S3 bucket. This use case is particularly valuable when handling sensitive data within an S3 bucket, and the intention is to restrict changes exclusively to privileged or MFA-authenticated users. For these privileged users, the additional security layer of multifactor authentication is enabled, ensuring a heightened level of access control and data protection.
The insights provided in this AWS IAM tutorial offer a comprehensive understanding of AWS security and IAM. Amazon Web Services extends a diverse array of remote computing services in addition to its security offerings. With the global adoption of AWS Cloud by businesses, there is a burgeoning demand for professionals equipped with profound knowledge of AWS principles and services.
The AWS Solution Architect Certification extensively explores critical facets of AWS Identity and Access Management (IAM), a pivotal service for ensuring security within AWS environments. This certification underscores the significance of gaining proficiency in IAM’s extensive features, enabling secure control over access to AWS services and resources. Embark on your AWS journey today with the Cloud Architect Course and position yourself for success in the realm of Amazon Web Services. If you’re looking to deepen your understanding and skills in IAM and other AWS concepts, consider enrolling in AWS Training in Pondicherry for comprehensive and hands-on learning experiences.
